Tag Archives: security
Log4J Zero-day Vulnerability and the U-M Response
In early December 2021, the world was faced with yet another massive zero-day vulnerability, when news broke that Log4j was being used to perform remote code execution and provide unauthorized access to servers. This vulnerability was quickly exploited to do everything from crypto-currency mining to ransomware installation. Log4j is a piece of open-source software used by numerous vendors… Read More »
Home for the holidays: Help conserve energy over break
As winter break approaches, many of us are busy with holiday plans and are eager to finish up our work so we can relax with family and friends. But before you set up your away message and head out the door: Help U-M conserve energy and money over the break: Close and lock all windows to save energy and prevent… Read More »
Coming soon: Changes to the Duo Mobile application interface
October is Cybersecurity Awareness Month!
Each October, ITS Information Assurance (IA) celebrates Cybersecurity Awareness Month by reminding members of the university community about their shared responsibility to protect themselves and the U-M community and by sharing IT security and privacy tips. “Cybersecurity, as a topic, a news item, and as an imperative is on the rise,” stated Sol Bermann, U-M Chief Information Security… Read More »
Hang up on phone scams
Checking systems for signs of compromise
Duo for U-M VPN coming this fall
Secure your devices
University makes changes to U-M Zoom
The university will roll out three key changes to U-M Zoom on May 18, 2021. The changes are being implemented to improve security while ensuring that U-M Zoom continues to meet the needs of the U-M community. Users of U-M Zoom are being notified of these changes on a rolling basis. It is important that users take action… Read More »
Success! Falcon endpoint protection deployment project complete
IT security is a shared responsibility and a never-ending journey of incremental improvement, but some improvements are larger and come faster than others. In October 2020, ITS announced that Enhanced Endpoint Protection powered by CrowdStrike Falcon would be rolled out to university-owned computers (desktops, laptops, and servers). About six months later, as of early March 2021, Falcon has… Read More »
Report IT security incidents
If you encounter an actual or suspected IT security incident, it is vital that you report it as soon as possible so that work can begin to investigate and resolve it. This applies whether you are working from home or on campus. Take a minute to watch the ITS Information Assurance (IA) video: How to Report an IT… Read More »
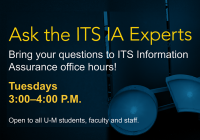
Ask the ITS IA Experts
Secure personal devices used with U-M data
Igo reviewed history of the SSN at Privacy Day webinar
CrowdStrike Falcon deployment in the homestretch
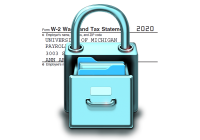
Tax fraud prevention tips
Beware! It’s that time of the year again! As you read this, criminals, fraudsters, and identity thieves could be working to file fraudulent tax returns in your name and steal your tax refund. ITS Information Assurance (IA) offers the following tips to help you protect yourself from identity theft and tax fraud: File your taxes as soon as… Read More »
Protect your U-M VPN connection with Duo
Securely dispose of your old tech
If you are adding or upgrading to new tech devices, you might have old ones that you, or U-M unit, are ready to dispose of. Old disks, flash drives, smartphones, and computers can all contain personal data, and in some cases, U-M data if you used those devices for work. Keep that data from falling into the wrong… Read More »
Home for the holidays? (Of course you are…)
Normally, we’d remind you about conserving energy and securing your desk and office before you leave campus for Winter Break. However, because many if not most of us are already working from home, we’re changing it up a bit this year. (But if you’re still in the office, check out last year’s article for details on what to… Read More »