Category Archives: Safe Computing
Protect privacy and practice online hygiene
Refreshed DCE101 Training: Cybersecurity and Data Protection at U-M
Tips for Traveling Safely with Technology
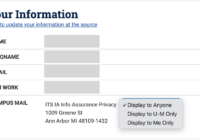
New MCommunity privacy setting for campus mailing address
Avoid scams that steal your login (and your paycheck!)
Scams that are designed to steal your login under false pretenses, such as a party invitation or a request to review a document, are affecting the U-M community. Please share this information with faculty, staff and students in your unit or department. How it works Scammers send you an email directing you to enter your uniqname, password, and… Read More »
Updated IT Standard on Network Security
Update Cookie Consent Integration by March 21
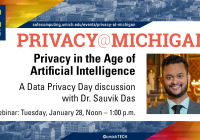
Celebrating Data Privacy Day 2025
Data Privacy Day event: Privacy in the Age of AI
IT Standard on Endpoint Security Administration
Stay Safe This Holiday Season
Secure Shopping Holiday Checklist
Beware of Multi-factor Authentication Scams
Protect Sensitive Data as AI Features Proliferate across Tech Industry
SUMIT Events Wrap-Up and Presentation Slides
LSA and ITS Information Assurance Expand Awareness of Scams Targeting Students
U-M Cloudflare Celebrates 1,000 Sites
More than 1,000 of the University of Michigan websites are protected with U-M Cloudflare, a significant milestone for the project implementation team. Cloudflare provides a critical security capability to protect university websites, web applications, and DNS (Domain Name System) servers from Distributed Denial of Service (DDoS) attacks and break-in or takeover attempts. Work continues to get more sites… Read More »